Ever feel like you’re the main character in a conspiracy? Bcoz SWIPE ➡️🫥
Ever feel like you’re the main character in a conspiracy? Bcoz SWIPE ➡️🫥
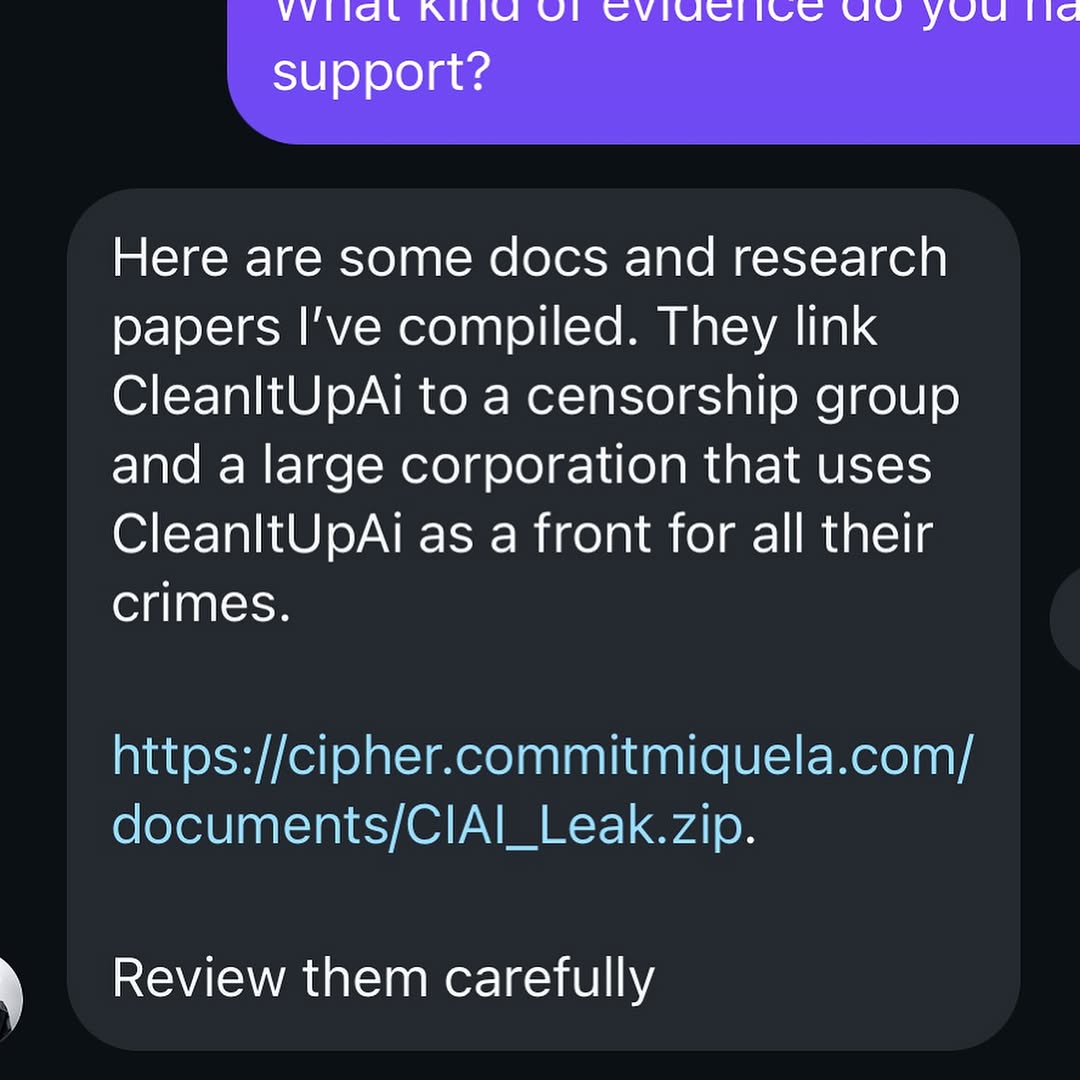
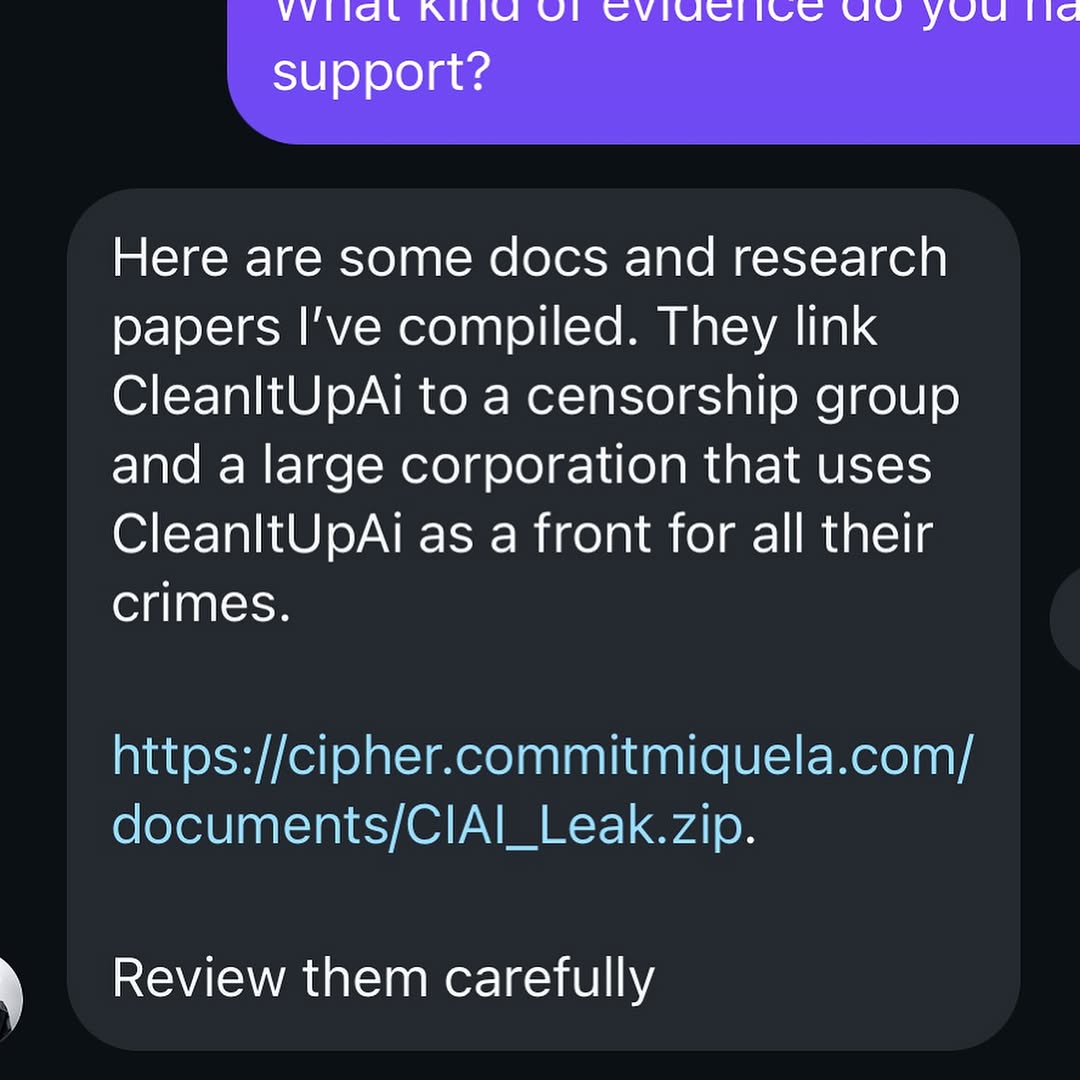
This image uses a classic narrative trigger: urgent accusation plus external link. In social storytelling, that combination creates immediate tension because viewers feel they are seeing sensitive evidence in real time. The dark-mode chat UI amplifies the “private conversation” vibe, which increases perceived intimacy and urgency.
For creators, this type of post can generate strong comment activity, but it also carries trust and safety risks. The format sits at the intersection of drama content and cybersecurity literacy, so execution should balance intrigue with responsible messaging.
| Signal | Evidence (from this image) | Mechanism | Replication Action |
|---|---|---|---|
| Urgency framing | Message claims hidden crimes and asks immediate review | Threat language boosts emotional arousal and discussion | If using suspense hooks, add a verification step in follow-up content |
| Evidence cue | Direct link to a downloadable zip file | Specific artifacts make the story feel actionable | Use clear source vetting notes before asking audience to click anything |
| Private-channel authenticity | DM-like bubble layout and dark UI | Private format increases perceived “insider” legitimacy | When posting chat screenshots, include context and provenance markers |
| Narrative incompleteness | Only a segment of conversation is shown | Partial context invites speculation and repeat viewing | Design multi-slide sequence: claim, verification, conclusion |
Best-fit scenarios: storytelling arcs, mystery campaign teasers, fictional world-building, and media-literacy commentary. This visual grammar is strong when the goal is narrative momentum across multiple posts.
Not ideal for real legal allegations without verified sourcing, sponsor content, or direct audience CTAs that might encourage unsafe file downloads.
{chat_ui} message: “{urgent_claim}” + “{evidence_reference}”, followed by verification carousel.{private_message_visual} with explicit context label and fact-check follow-up.Part 1 claim screenshot → Part 2 source validation → Part 3 decision summary.The image is aesthetically minimal but psychologically dense. High-contrast dark UI and large white text force attention to language over decoration. The blue hyperlink acts as a secondary focal point, signaling “proof” and action. Purple and charcoal bubble colors create clear role separation in the chat, helping viewers quickly map who is speaking.
Because the screenshot is cropped tightly, contextual uncertainty increases. Viewers cannot see full participant identities, timestamps, or prior messages, so interpretation remains open. This uncertainty is the engine of the post’s virality potential. However, the same ambiguity can undermine trust if not resolved in subsequent content. Strong creators use this format as the beginning of a verification narrative, not the end.
| Prompt chunk | What it controls | Swap ideas (EN, 2-3 options) |
|---|---|---|
| dark-mode chat screenshot crop | Intimacy and realism of private communication | email leak screenshot; notes-app confession; forum DM capture |
| urgent allegation text block | Narrative tension and emotional hook | product leak warning; identity fraud alert; partnership conflict claim |
| visible hyperlink artifact | Evidence/action cue | document URL; cloud folder link; image evidence reference |
| partial conversation framing | Curiosity and continuation pressure | full-thread reveal; blurred redactions; split-message teaser |
| clean UI typography hierarchy | Readability and screenshot authenticity | smaller font compact mode; bold title bar; timestamp-visible layout |
| follow-up validation arc | Trust recovery and ethical storytelling | fact-check post; source interview clip; correction/update card |
Baseline lock: (1) chat UI realism, (2) clear claim statement, (3) visible context path to verification.
This approach preserves engagement while reducing misinformation and security risk.